Digilink SOC 2 Compliance - Secured Network Smart Lock Management Solution
Business professionals around the world are continuously learning about the importance of information security, cybersecurity, and the need to protect the physical, digital, and information assets used to successfully conduct business. A commonly known way for individuals and organizations to understand whether they can trust an online service includes confirming that the online service provider has received a Systems and Organizations Control (SOC) report.
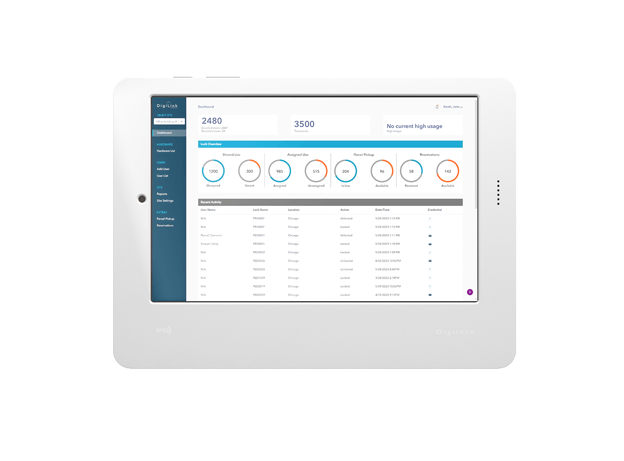
Digilock has received a SOC 2 Type II report for its Digilink Smart Lock Management System, demonstrating the effective implementation of security practices to provide a secure web application product and protect customer data.
What Is A SOC 2 Report?
There are many organizations in the world that have developed standards for the appropriate safeguarding and protection of information. One of the most commonly known security standards used in the world today includes SOC reporting standards, issued by the American Institute of Certified Public Accountants (AICPA).
A SOC report communicates state of operations for a service or product that is provided by an organization, referred to in SOC compliance as a “Service Organization”, and includes a wealth of information describing the covered service or product and its related operations and/or security practices.
There are several types of SOC reports that can be issued for a Service Organization, including SOC 1, SOC 2, and SOC 3 reports, among others. Management of Service Organization, like Digilock, make the decisions on the type of SOC report that is required for their organization and the users of their system and service offerings.
A SOC 2 report has a primary focus on the security related to a product or service and provides users of the product or service with a comprehensive understanding of security practices implemented by the Service Organization to protect the data and information technology resources that operate the product or service.
Understanding Type I vs Type II
SOC reports are issued with associated “types”, which communicate the extent to which a user of the SOC report can rely on the report’s information:
- Type I - A Type 1 report provides an auditor’s opinion on the “design” of the security practices implemented for a product or service at one point in time (as of a specified date), but provides no opinion on the operation of these security practices over a period of time. Although Type 1 report is a good step to demonstrating appropriate security, it does not provide as much assurance as a Type 2 report.
- Type II - A Type 2 report provides an auditor’s opinion on the “design and operation” of the security practices implemented for a product or service over a period of time. A SOC 2 report provides the most assurance about the security practices of a Service Organization, and results from the completion of a thorough audit (examination) of the Service Organization’s security practices for the product or service to validate that security practices were performed for a period of time (typically 6 months or a year).
A Smart Lock Management Solution You Can Trust
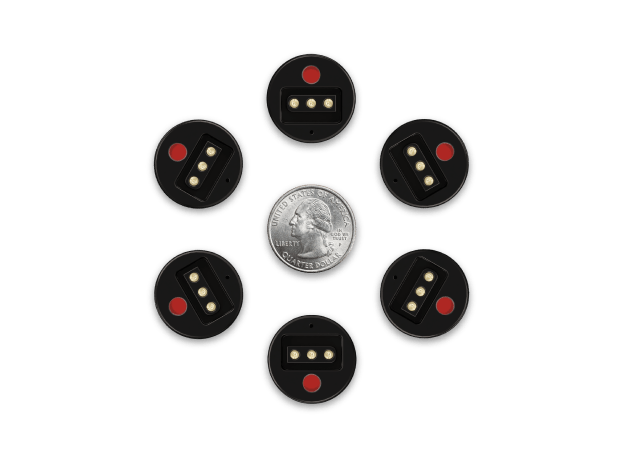
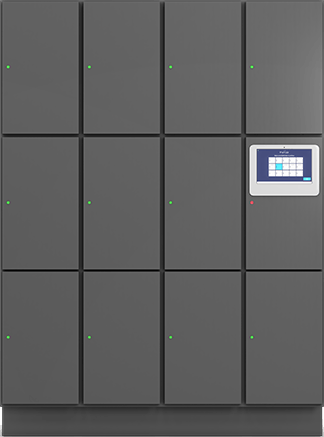
With our Digilink Smart Lock Management System, we provide our customers with a smart lock management solution that contributes to the physical security component of an improved network security and cybersecurity posture. Using Digilink, our customers can manage the locking and unlocking security for storage locations within their organization. This contributes to securing confidential or sensitive information and assets that need to be protected from unauthorized access. Digilink collects and stores data that is needed to enable system use. Our customers provide their data and expect that we will protect it as it lives within our environment.
The receipt of SOC 2 Type II certification demonstrates that we protect customer information during the information processing lifecycle of our Digilink web application, and our customers can trust that their data is reasonably protected from security threats that may lead to data breaches or security compromises that would inappropriately disclose or divulge their information.
Request A Copy Of Our Digilink SOC 2 Report
Our SOC 2 report is available to Digilink customers upon request. Please contact our customer service team or your account manager to request a copy of our SOC 2 Type II report.